Airport X-Ray Scanners Can be Hacked to Mask Weapons
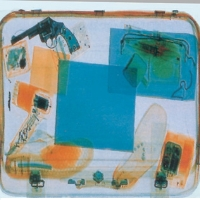
Scanners used at airport security checkpoints can be infiltrated and manipulated to fool Transportation Security Administration (TSA) screeners into seeing false images, according to security experts.
The potential vulnerability in the machines (Rapiscan 522B) could result in terrorists smuggling weapons through checkpoints and boarding planes with them.
Billy Rios and Terry McCorkle, who work for the security firm Qualys, discovered the flaw in the Rapiscan’s software.
They said the trouble lies within the equipment’s Threat Image Projection (TIP) function, which allows supervisors to train and test TSA screeners by superimposing fake images inside luggage being x-rayed.
But a hacker could use this same training function to trick agents into seeing, for example, a pair of socks instead of a handgun hidden inside a suitcase.
“Someone could basically own this machine and modify the images that the operators see,” Rios told Wired.
Rios and his colleague also discovered that hackers can access the machine’s system without needing a TSA supervisor’s password.
Wired’s Kim Zetter wrote that “the supervisor’s password screen could be subverted through a simple SQL injection attack — a common hacker tactic that involves entering a special string of characters to trigger a system into doing something it shouldn’t do. In this case, the string would allow an attacker to bypass the login to gain access to a console screen that controls the TIP feature.”
“Just throw [these] characters into the login,” Rios said, and the system accepts it. “It tells you there’s an error, [but then] just logs you in.”
The hacker would then be free to superimpose an image of a harmless item, masking the visibility of one that could be threatening to the aircraft, such as a gun or an explosive.
Rapiscan responded to the security experts’ claims by denying their machines have password vulnerability and that images can be superimposed; they suggested that Rios and McCorkle used misconfigured equipment. TSA also chimed in, claiming that it would have been impossible for them to have acquired the software that the agency uses in the scanners.
“The Rapiscan version that is utilized by TSA is not available for sale commercially or to any other entity; the commercial version of the TIP software is not used by TSA,” TSA spokesman Ross Feinstein told Wired.
Rios insisted his team’s research is solid, adding that Rapiscan failed to encrypt operator data in the scanner’s system, which facilitates hacking. “It’s so outrageous that they didn’t [encrypt]. If anyone ever gets access to the [Rapiscan] file system, they will have access to all the user accounts and passwords in clear text,” he told Wired. “No need for keyloggers or malware, just read them out of the text files.”
The Rapiscan system that Rios and McCorkle used in their research was purchased second-hand for $300 from an online seller in California. They normally sell for up to $20,000 in surplus.
-Noel Brinkerhoff, Danny Biederman
To Learn More:
Hacked X-Rays Could Slip Guns Past Airport Security (by Kim Zetter, Wired)
Clerical Blunder Reveals TSA Considers Airport Terrorist Attack Unlikely (by Noel Brinkerhoff, AllGov)
Body Scanners Create Profits for Chertoff and Others (by Noel Brinkerhoff, AllGov)
- Top Stories
- Unusual News
- Where is the Money Going?
- Controversies
- U.S. and the World
- Appointments and Resignations
- Latest News
- Trump Orders ICE and Border Patrol to Kill More Protestors
- Trump Renames National Football League National Trump League
- Trump to Stop Deportations If…
- Trump Denounces World Series
- What If China Invaded the United States?






Comments