Tracking Cell Phone SIM Cards Is Key to NSA Role in U.S. Drone Strikes
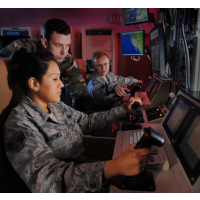 U.S. drone control station (photo: U.S. Air Force)
U.S. drone control station (photo: U.S. Air Force)
Before the United States launches a drone strike on a terrorist threat, it turns to the National Security Agency (NSA) to locate the person, which often entails tracking the terrorist’s cell phone and its memory (SIM) card. But this approach to identifying targets has proven fallible because it can be deadly for innocent bystanders and others not on the U.S. kill list.
When it comes to finding foreign threats, the government has two primary means of intelligence: human and electronic. The latter is demonstrated by the use of SIM cards to find targets for drone strikes.
Human-based intelligence gathering has often been employed to more accurately find and confirm a target’s location before carrying out a deadly attack.
But the U.S. drone program often foregoes waiting for on-the-ground confirmation from human sources before giving the order to take out a threat.
Instead, it relies solely on the NSA to tell drone operators where someone is located based on data intercepted from their cell phone. This strategy fails to take into account that pinpointing the exact longitude and latitude of a SIM card doesn’t mean the person holding it is the al Qaeda or Taliban member wanted dead by the U.S.
“Some top Taliban leaders, knowing of the NSA’s targeting method, have purposely and randomly distributed SIM cards among their units in order to elude their trackers,” Jeremy Scahill and Glenn Greenwald wrote at The Intercept, a new investigative journalism website.
“They would do things like go to meetings, take all their SIM cards out, put them in a bag, mix them up, and everybody gets a different SIM card when they leave,” a former drone operator who wished to remain anonymous told The Intercept. “That’s how they confuse us.”
The drone operator added: “Once the bomb lands or a night raid happens, you know that phone is there. But we don’t know who’s behind it, who’s holding it. It’s of course assumed that the phone belongs to a human being who is nefarious and considered an ‘unlawful enemy combatant.’ This is where it gets very shady.”
-Noel Brinkerhoff
To Learn More:
The NSA’s Secret Role in the U.S. Assassination Program (by Jeremy Scahill and Glenn Greenwald, The Intercept)
NSA Collaborates with CIA in Drone Assassination Program; Post Redacts Details at Obama Administration’s Request (by Noel Brinkerhoff and Danny Biederman, AllGov)
- Top Stories
- Unusual News
- Where is the Money Going?
- Controversies
- U.S. and the World
- Appointments and Resignations
- Latest News
- Trump Kidnaps Gov. Newsom and His Wife
- Trump Orders ICE and Border Patrol to Kill More Protestors
- Trump Renames National Football League National Trump League
- Trump to Stop Deportations If…
- Trump Denounces World Series






Comments